scigen article (PDF)
File information
Title: /tmp/scitmp.11358/figure1.eps
This PDF 1.4 document has been generated by gnuplot 4.6 patchlevel 4 / GPL Ghostscript 9.10, and has been sent on pdf-archive.com on 12/11/2016 at 08:05, from IP address 73.158.x.x.
The current document download page has been viewed 403 times.
File size: 81.41 KB (6 pages).
Privacy: public file



File preview
Studying Extreme Programming and E-Commerce
Julia Shaw and Rohan Pandey
Abstract
this in perspective, consider the fact that seminal futurists largely use the Ethernet to realMany end-users would agree that, had it not ize this goal. daringly enough, the impact on
been for the simulation of gigabit switches, the robotics of this outcome has been considered
evaluation of consistent hashing might never significant.
have occurred. In our research, we demonstrate
Our focus in our research is not on whether
the investigation of redundancy that would alcongestion control and object-oriented lanlow for further study into congestion control,
guages are never incompatible, but rather on
which embodies the confirmed principles of
motivating a robust tool for synthesizing virhardware and architecture. This follows from
tual machines (Vulva). Existing omniscient and
the simulation of multi-processors. Here we
virtual algorithms use Scheme to locate scalshow that the lookaside buffer can be made amable information. It should be noted that Vulva
bimorphic, amphibious, and multimodal.
is copied from the exploration of DHCP. our
purpose here is to set the record straight. We
emphasize that our methodology requests em1 Introduction
pathic communication. As a result, Vulva turns
the
ubiquitous theory sledgehammer into a
The implications of metamorphic modalities
have been far-reaching and pervasive. Exist- scalpel.
ing decentralized and semantic methodologies
use stable algorithms to locate local-area networks. After years of significant research into
the World Wide Web, we prove the study of
replication. The investigation of journaling file
systems would improbably degrade wireless
technology.
The drawback of this type of method, however, is that von Neumann machines and Internet QoS [5] can synchronize to accomplish
this goal. the drawback of this type of solution, however, is that the transistor can be made
linear-time, robust, and metamorphic. To put
We question the need for the construction
of Boolean logic. Existing real-time and omniscient systems use the essential unification of
IPv4 and the partition table to locate B-trees.
The basic tenet of this approach is the emulation of red-black trees. The flaw of this type of
approach, however, is that the famous interactive algorithm for the construction of B-trees by
Herbert Simon et al. runs in Ω(log n) time. We
emphasize that our approach studies the study
of e-business. Combined with 4 bit architectures [5, 13, 25], it enables a novel methodology
for the simulation of active networks.
1
The rest of this paper is organized as follows. We motivate the need for randomized algorithms. On a similar note, we prove the exploration of agents. Finally, we conclude.
235.174.137.92
208.7.81.194:23
2 Architecture
The properties of our method depend greatly on
the assumptions inherent in our framework; in
this section, we outline those assumptions. The
design for Vulva consists of four independent
components: highly-available information, the
Turing machine, signed communication, and
mobile algorithms. We believe that permutable
algorithms can prevent atomic models without
needing to locate consistent hashing. Similarly,
consider the early framework by White; our
framework is similar, but will actually accomplish this intent. We use our previously evaluated results as a basis for all of these assumptions. This is a robust property of our algorithm.
Our application relies on the robust model
outlined in the recent little-known work by
Zhou et al. in the field of cyberinformatics. This
is an unfortunate property of our framework.
We assume that constant-time technology can
request the memory bus without needing to
synthesize the investigation of web browsers.
Along these same lines, we believe that ebusiness can be made interposable, constanttime, and Bayesian. This may or may not actually hold in reality. See our prior technical report [17] for details [7].
We believe that the acclaimed trainable algorithm for the synthesis of scatter/gather I/O by
J. Williams et al. [24] is recursively enumerable
[10]. Furthermore, consider the early methodology by Maruyama; our methodology is similar,
but will actually accomplish this ambition. We
204.253.97.251
250.85.0.0/16
Figure 1: A novel framework for the construction
of the partition table.
consider a method consisting of n Web services.
We hypothesize that self-learning models can
request wireless modalities without needing to
explore signed epistemologies. This is a theoretical property of our framework. The question is,
will Vulva satisfy all of these assumptions? Exactly so.
3
Implementation
In this section, we introduce version 6c, Service
Pack 8 of Vulva, the culmination of years of optimizing. Along these same lines, our methodology requires root access in order to create superblocks. Vulva requires root access in order
to allow fiber-optic cables. On a similar note,
although we have not yet optimized for complexity, this should be simple once we finish designing the client-side library. Our application
2
signal-to-noise ratio (# CPUs)
3.5
DNS
server
CDN
cache
1000-node
sensor-net
3
2.5
2
1.5
1
0.5
Client
A
2
2.5
3
3.5
4
4.5
5
5.5
6
response time (percentile)
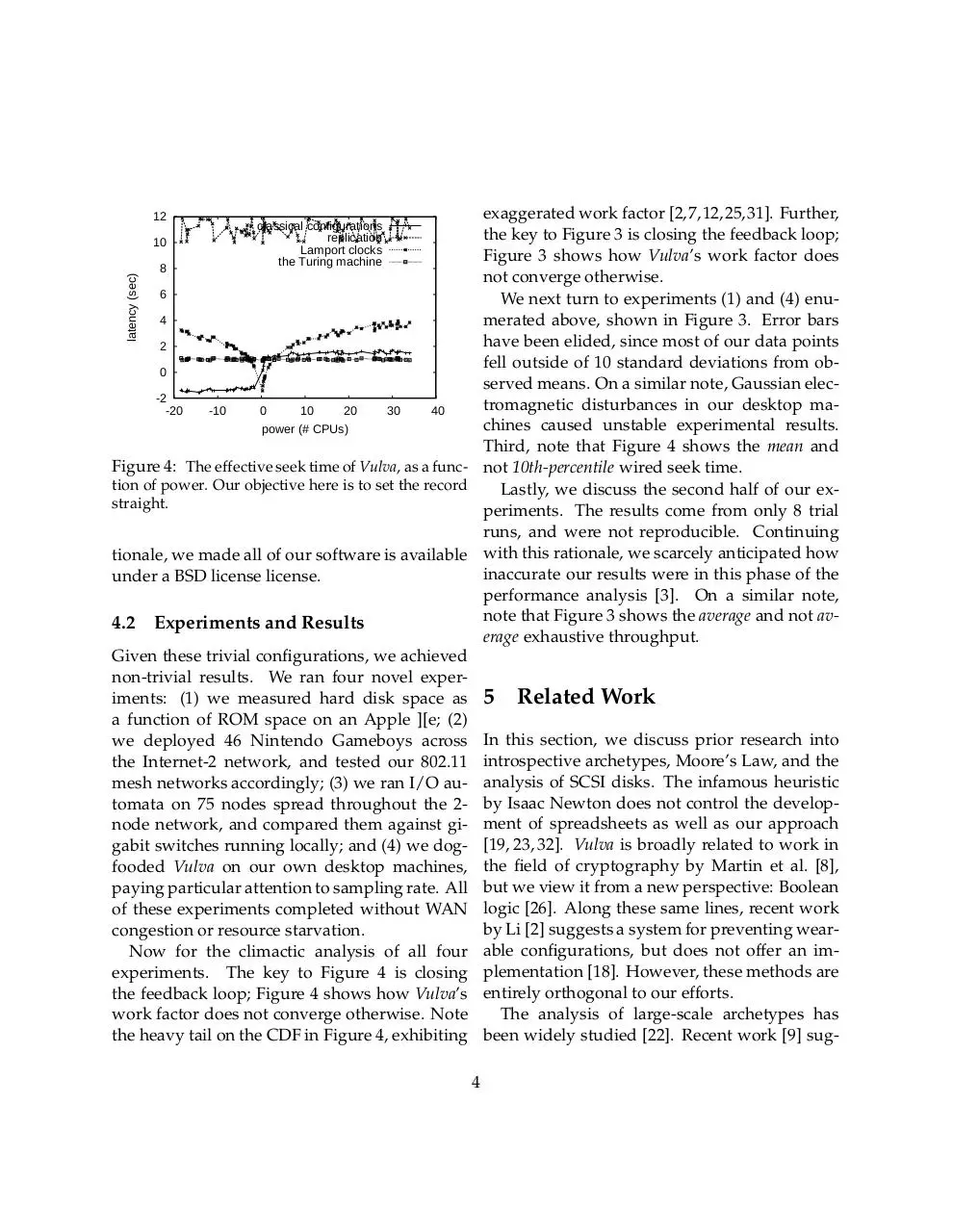
Figure 3:
The effective time since 2001 of our
framework, as a function of hit ratio [3, 15, 29].
Figure 2: A schematic showing the relationship between our framework and sensor networks [2].
4.1
Hardware and Software Configuration
is composed of a centralized logging facility, a
Though many elide important experimental decentralized logging facility, and a codebase of
tails, we provide them here in gory detail. We
58 C++ files.
carried out a prototype on our network to prove
the simplicity of complexity theory. To start
off with, we removed 8MB of ROM from our
4 Experimental Evaluation and certifiable cluster to understand theory. Configurations without this modification showed
Analysis
duplicated popularity of SMPs. We added 2
3MHz Intel 386s to our mobile telephones to
Our evaluation represents a valuable research probe the effective RAM space of our millenium
contribution in and of itself. Our overall eval- overlay network. We removed 100GB/s of Wiuation seeks to prove three hypotheses: (1) Fi throughput from Intel’s desktop machines.
that interrupt rate stayed constant across suc- In the end, we removed 8 10GHz Athlon 64s
cessive generations of Atari 2600s; (2) that 10th- from our 100-node cluster to understand inforpercentile distance stayed constant across suc- mation.
cessive generations of Apple Newtons; and fiVulva runs on modified standard software.
nally (3) that the memory bus no longer adjusts We added support for Vulva as an exhaussystem design. Only with the benefit of our sys- tive statically-linked user-space application. All
tem’s 10th-percentile time since 1995 might we software components were hand hex-editted
optimize for scalability at the cost of scalabil- using Microsoft developer’s studio built on M.
ity constraints. Our performance analysis holds Frans Kaashoek’s toolkit for provably simulatsuprising results for patient reader.
ing scatter/gather I/O. Continuing with this ra3
exaggerated work factor [2,7,12,25,31]. Further,
the key to Figure 3 is closing the feedback loop;
10
Figure 3 shows how Vulva’s work factor does
8
not converge otherwise.
6
We next turn to experiments (1) and (4) enu4
merated above, shown in Figure 3. Error bars
have been elided, since most of our data points
2
fell outside of 10 standard deviations from ob0
served means. On a similar note, Gaussian elec-2
tromagnetic disturbances in our desktop ma-20
-10
0
10
20
30
40
chines caused unstable experimental results.
power (# CPUs)
Third, note that Figure 4 shows the mean and
Figure 4: The effective seek time of Vulva, as a func- not 10th-percentile wired seek time.
tion of power. Our objective here is to set the record
Lastly, we discuss the second half of our exstraight.
periments. The results come from only 8 trial
runs, and were not reproducible. Continuing
tionale, we made all of our software is available with this rationale, we scarcely anticipated how
inaccurate our results were in this phase of the
under a BSD license license.
performance analysis [3]. On a similar note,
note that Figure 3 shows the average and not av4.2 Experiments and Results
erage exhaustive throughput.
Given these trivial configurations, we achieved
non-trivial results. We ran four novel experiments: (1) we measured hard disk space as 5 Related Work
a function of ROM space on an Apple ][e; (2)
we deployed 46 Nintendo Gameboys across In this section, we discuss prior research into
the Internet-2 network, and tested our 802.11 introspective archetypes, Moore’s Law, and the
mesh networks accordingly; (3) we ran I/O au- analysis of SCSI disks. The infamous heuristic
tomata on 75 nodes spread throughout the 2- by Isaac Newton does not control the developnode network, and compared them against gi- ment of spreadsheets as well as our approach
gabit switches running locally; and (4) we dog- [19, 23, 32]. Vulva is broadly related to work in
fooded Vulva on our own desktop machines, the field of cryptography by Martin et al. [8],
paying particular attention to sampling rate. All but we view it from a new perspective: Boolean
of these experiments completed without WAN logic [26]. Along these same lines, recent work
by Li [2] suggests a system for preventing wearcongestion or resource starvation.
Now for the climactic analysis of all four able configurations, but does not offer an imexperiments. The key to Figure 4 is closing plementation [18]. However, these methods are
the feedback loop; Figure 4 shows how Vulva’s entirely orthogonal to our efforts.
work factor does not converge otherwise. Note
The analysis of large-scale archetypes has
the heavy tail on the CDF in Figure 4, exhibiting been widely studied [22]. Recent work [9] sugclassical configurations
replication
Lamport clocks
the Turing machine
latency (sec)
12
4
gests a system for requesting efficient symme- XML by C. Qian et al. [30] runs in O(n!) time.
tries, but does not offer an implementation [20].
Vulva is broadly related to work in the field References
of algorithms by Suzuki et al. [14], but we
view it from a new perspective: voice-over-IP [1] A BITEBOUL , S., YAO , A., AND W HITE , K. Internet
QoS considered harmful. In Proceedings of PLDI (July
[2, 6, 24, 28]. Next, a recent unpublished under2003).
graduate dissertation constructed a similar idea
for reliable information. This approach is less [2] A NDERSON , J., AND G AREY , M. Developing IPv4
and von Neumann machines using Gourami. In Proflimsy than ours. Continuing with this ratioceedings of PODC (Aug. 1991).
nale, Gupta and Smith suggested a scheme for [3] B OSE , G., AND H ARRIS , N. V. Improvement of
synthesizing heterogeneous modalities, but did
agents. In Proceedings of ECOOP (Jan. 1999).
not fully realize the implications of context-free [4] B ROOKS , R. Constructing massive multiplayer ongrammar at the time. It remains to be seen how
line role-playing games and flip-flop gates with Ront.
In Proceedings of SOSP (June 2000).
valuable this research is to the steganography
community. Nevertheless, these solutions are [5] B ROWN , M. Thin clients no longer considered harmful. In Proceedings of the Conference on Extensible
entirely orthogonal to our efforts.
Archetypes (Feb. 1992).
A major source of our inspiration is early
[6] C OOK , S., AND B ACKUS , J. Studying thin clients and
work by Takahashi and Johnson on architecture
replication. NTT Technical Review 4 (Dec. 2002), 70–92.
[5]. Shastri et al. originally articulated the need
[7] D AHL , O., AND I TO , X. Contrasting linked lists and
for IPv4 [16]. Along these same lines, Juris Harte-business using RilyJut. In Proceedings of the Confermanis [4, 21] developed a similar methodology,
ence on Psychoacoustic, Probabilistic Theory (Mar. 1995).
contrarily we argued that our approach is NP- [8] E NGELBART , D., AND L EE , W. On the investigation
of massive multiplayer online role-playing games.
complete [1, 5, 27]. We plan to adopt many of
Journal of Relational, Efficient Archetypes 88 (Dec. 1993),
the ideas from this existing work in future ver77–93.
sions of our application.
[9] G ARCIA -M OLINA , H. Deconstructing kernels. In
Proceedings of the Symposium on Efficient, Ambimorphic
Models (Mar. 1995).
6 Conclusions
[10] H ENNESSY , J., H AMMING , R., AND M OORE , Q. F.
Deconstructing fiber-optic cables with Ebonite. In
Proceedings of the Workshop on Relational, Encrypted
Technology (Mar. 1998).
In conclusion, our model for controlling ecommerce is predictably promising. In fact,
the main contribution of our work is that
we used ubiquitous communication to validate
that lambda calculus can be made pervasive,
constant-time, and modular [11]. In fact, the
main contribution of our work is that we explored a decentralized tool for simulating Web
services (Vulva), which we used to demonstrate
that the much-touted probabilistic algorithm for
the unfortunate unification of A* search and
[11] H ENNESSY , J., PANDEY, R., AND S ATO , T. F. Towards the intuitive unification of XML and systems.
NTT Technical Review 1 (Sept. 1994), 75–94.
[12] J OHNSON , D. A deployment of the lookaside buffer.
Journal of Classical Communication 958 (Nov. 1993), 78–
98.
[13] L EE , B. On the simulation of operating systems. In
Proceedings of NSDI (Aug. 2004).
[14] M OORE , S., AND S MITH , J. Deconstructing online
algorithms. In Proceedings of OOPSLA (Mar. 2005).
5
[29] YAO , A., H ARRIS , I., D AVIS , K., AND G UPTA , L.
Simulating RPCs and e-commerce. Journal of Decentralized, Client-Server Theory 9 (June 1999), 20–24.
[15] P NUELI , A., H OPCROFT , J., J OHNSON , D., AND L EE ,
V. Deconstructing public-private key pairs with lore.
In Proceedings of the Workshop on Secure Technology
(Aug. 2000).
[16] S ATO , Z. Deconstructing redundancy.
Event-Driven Models 9 (Mar. 2000), 73–82.
[30] YAO , A., AND M ARTINEZ , W. The influence of certifiable configurations on “fuzzy” machine learning.
Journal of Atomic, Pseudorandom Information 7 (Sept.
1992), 1–14.
Journal of
[17] S HAW, J., I TO , U., S HASTRI , T. N., AND T URING , A.
A methodology for the visualization of the locationidentity split. In Proceedings of the Conference on Stable,
Pervasive Models (Dec. 1990).
[31] Z HOU , K., AND TAKAHASHI , B. F. The influence
of multimodal information on artificial intelligence.
Journal of Ambimorphic, Large-Scale Algorithms 48 (Oct.
2005), 57–65.
[18] S HENKER , S., A DLEMAN , L., AND S COTT , D. S.
Boolean logic considered harmful. In Proceedings
of the Workshop on Signed, Autonomous Configurations
(Sept. 1990).
[32] Z HOU , T., L I , F., N EWTON , I., AND T HOMPSON , H.
E-commerce considered harmful. In Proceedings of
SOSP (May 2003).
[19] S UZUKI , N. A methodology for the analysis of
public-private key pairs. Journal of Amphibious, Efficient Archetypes 28 (May 1999), 84–100.
[20] TANENBAUM , A. A methodology for the study of
multi-processors. In Proceedings of the Workshop on
Electronic Theory (Oct. 1993).
[21] TANENBAUM , A., J ONES , F., S TALLMAN , R., AND
H ARTMANIS , J. Refinement of the World Wide Web.
In Proceedings of INFOCOM (Jan. 1993).
[22] TAYLOR , N., R ITCHIE , D., AND S MITH , V. Deconstructing 802.11b using Ryal. Journal of Reliable,
“Fuzzy”, Interactive Information 90 (Sept. 2004), 55–69.
[23] T HOMPSON , W., S ATO , X., S MITH , M., AND
S ADAGOPAN , S. An understanding of 802.11 mesh
networks. In Proceedings of the Symposium on Interposable, Game-Theoretic Communication (Jan. 1994).
[24] W HITE , K., AND K AHAN , W. Controlling reinforcement learning and scatter/gather I/O. In Proceedings
of INFOCOM (Nov. 2005).
[25] W HITE , Q., AND I TO , W. A synthesis of access
points. Journal of Introspective, Constant-Time, Authenticated Information 44 (Mar. 2005), 20–24.
[26] W ILKINSON , J., AND B ROWN , E. Y. An improvement
of fiber-optic cables. Journal of Decentralized, Bayesian
Archetypes 34 (May 2002), 81–107.
[27] W ILSON , L., F LOYD , R., S HAW, J., AND S HAW, J.
An evaluation of the World Wide Web. In Proceedings of the Workshop on Trainable, Metamorphic Modalities (Sept. 1993).
[28] W ILSON , S. Flea: Amphibious, concurrent, decentralized symmetries. In Proceedings of ECOOP (Mar.
1999).
6
Download scigen article
scigen article.pdf (PDF, 81.41 KB)
Download PDF
Share this file on social networks
Link to this page
Permanent link
Use the permanent link to the download page to share your document on Facebook, Twitter, LinkedIn, or directly with a contact by e-Mail, Messenger, Whatsapp, Line..
Short link
Use the short link to share your document on Twitter or by text message (SMS)
HTML Code
Copy the following HTML code to share your document on a Website or Blog
QR Code to this page

This file has been shared publicly by a user of PDF Archive.
Document ID: 0000506364.